- ANS-123 AMSAT News Service Bulletins
- Free ARRL Events App Now Live for 2026 Dayton Hamvention®
- FCC Approves Limited Emergency Use of 70 cm Band by AST SpaceMobile Satellites Outside the US
- New Book Release: Satellite Operating for Amateur Radio
- 2025 Bill Orr, W6SAI, Technical Writing Winners Awarded
You are here
Technology
TWiT 1082: Hanging by a Thread - Are We Headed for a Tech Crash or a Golden Age?
Big Tech is pouring hundreds of billions into AI, but with rising signs of an industry bubble and some real-world fallout, this week's episode digs into who actually wins, who stands to lose, and whether Apple's patient strategy may outsmart the hype.
- Big Tech firms beat earnings expectations amid AI spending questions
- RIP the $599 Mac Mini, you were too beautiful for this world
- Microsoft lifts 2026 AI spend by $25 billion to cover component price rises
- Microsoft speeds up in Big Tech's data center spend-off
- Crosswording the Situation
- Meta's historic loss in court could cost a lot more than $375 million
- Utah first state to hold websites liable for users who mask their location with VPNs — law goes into effect, designed to prevent bypassing age checks
- Australia unveils a 2.25% levy on Meta, Google, and TikTok
- Meta found in breach of EU law for failing to keep children off Facebook and Instagram
- Meta inks deal for solar power at night, beamed from space
- Musk v. Altman week 1: Elon Musk says he was duped, warns AI could kill us all, and admits that xAI distills OpenAI's models
- OpenAI-backed 1X opens California factory targeting 10,000 home humanoid robots in year one
- Sam Altman asked GPT-5.5 to plan its own launch party. Its requests were 'beautiful' but 'strange.'
- Sam Altman says Elon Musk can come to his GPT 5.5 party: 'World needs more love'
- The US Senate unanimously passed a rule barring senators from trading on prediction markets like
- Kalshi and Polymarket, amid rising concern over insider trading
- 'We Know You Live Right Here': No Secrets in America's New Surveillance Dragnet
- California to begin ticketing driverless cars that violate traffic laws
- China Suspends New Autonomous Driving Permits After Baidu Outage
- China has decided that firing a worker because an AI can do their job is illegal. No Western country has done the same.
- Maryland Is First to Ban A.I.-Driven Price Increases in Grocery Stores
- The most severe Linux threat to surface in years catches the world flat-footed
- Hackers are actively exploiting a bug in cPanel, used by millions of websites
- The Hottest Anti-AI Gadget Is a Cyberdeck
- Jack Dorsey-backed Vine reboot Divine launches to the public
- GameStop eyes eBay takeover in audacious $46 billion bet on Ryan Cohen's e-commerce vision
- AI-generated actors and scripts are now ineligible for Oscars
- Ukraine says it's training drone pilots in 'Grand Theft Auto V'
- This free website is like Wikipedia meets the CIA
- Light Phone III Is a Delightfully Minimalist Smartphone Alternative
- Valve Steam Controller is here, it's a gamepad in search of a console
- Bluetooth Connected - The Voices Behind the Connection
- Spirit Airlines shuts down after Trump's war on Iran doubled jet fuel prices
- Ask.com has shut down, marking the official farewell to the Internet's favorite butler
- Pioneering geneticist and decoder of the human genome J. Craig Venter dies at age 79
Host: Leo Laporte
Guests: Nicholas De Leon, Devindra Hardawar, and Mikah Sargent
Download or subscribe to This Week in Tech at https://twit.tv/shows/this-week-in-tech
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
Anti-DDoS Firm Heaped Attacks on Brazilian ISPs
A Brazilian tech firm that specializes in protecting networks from distributed denial-of-service (DDoS) attacks has been enabling a botnet responsible for an extended campaign of massive DDoS attacks against other network operators in Brazil, KrebsOnSecurity has learned. The firm’s chief executive says the malicious activity resulted from a security breach and was likely the work of a competitor trying to tarnish his company’s public image.

An Archer AX21 router from TP-Link. Image: tp-link.com.
For the past several years, security experts have tracked a series of massive DDoS attacks originating from Brazil and solely targeting Brazilian ISPs. Until recently, it was less than clear who or what was behind these digital sieges. That changed earlier this month when a trusted source who asked to remain anonymous shared a curious file archive that was exposed in an open directory online.
The exposed archive contained several Portuguese-language malicious programs written in Python. It also included the private SSH authentication keys belonging to the CEO of Huge Networks, a Brazilian ISP that primarily offers DDoS protection to other Brazilian network operators.
Founded in Miami, Fla. in 2014, Huge Networks’s operations are centered in Brazil. The company originated from protecting game servers against DDoS attacks and evolved into an ISP-focused DDoS mitigation provider. It does not appear in any public abuse complaints and is not associated with any known DDoS-for-hire services.
Nevertheless, the exposed archive shows that a Brazil-based threat actor maintained root access to Huge Networks infrastructure and built a powerful DDoS botnet by routinely mass-scanning the Internet for insecure Internet routers and unmanaged domain name system (DNS) servers on the Web that could be enlisted in attacks.
DNS is what allows Internet users to reach websites by typing familiar domain names instead of the associated IP addresses. Ideally, DNS servers only provide answers to machines within a trusted domain. But so-called “DNS reflection” attacks rely on DNS servers that are (mis)configured to accept queries from anywhere on the Web. Attackers can send spoofed DNS queries to these servers so that the request appears to come from the target’s network. That way, when the DNS servers respond, they reply to the spoofed (targeted) address.
By taking advantage of an extension to the DNS protocol that enables large DNS messages, botmasters can dramatically boost the size and impact of a reflection attack — crafting DNS queries so that the responses are much bigger than the requests. For example, an attacker could compose a DNS request of less than 100 bytes, prompting a response that is 60-70 times as large. This amplification effect is especially pronounced when the perpetrators can query many DNS servers with these spoofed requests from tens of thousands of compromised devices simultaneously.
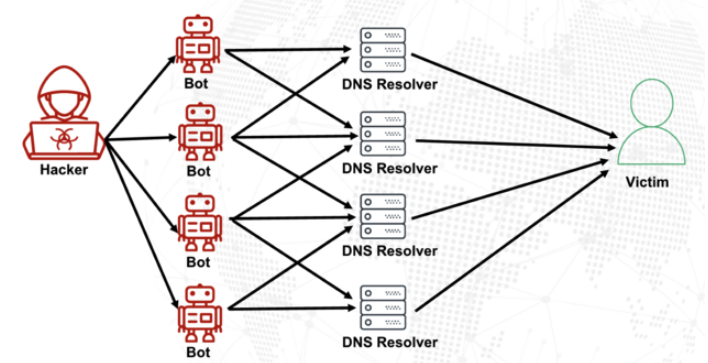
A DNS amplification and reflection attack, illustrated. Image: veracara.digicert.com.
The exposed file archive includes a command-line history showing exactly how this attacker built and maintained a powerful botnet by scouring the Internet for TP-Link Archer AX21 routers. Specifically, the botnet seeks out TP-Link devices that remain vulnerable to CVE-2023-1389, an unauthenticated command injection vulnerability that was patched back in April 2023.
Malicious domains in the exposed Python attack scripts included DNS lookups for hikylover[.]st, and c.loyaltyservices[.]lol, both domains that have been flagged in the past year as control servers for an Internet of Things (IoT) botnet powered by a Mirai malware variant.
The leaked archive shows the botmaster coordinated their scanning from a Digital Ocean server that has been flagged for abusive activity hundreds of times in the past year. The Python scripts invoke multiple Internet addresses assigned to Huge Networks that were used to identify targets and execute DDoS campaigns. The attacks were strictly limited to Brazilian IP address ranges, and the scripts show that each selected IP address prefix was attacked for 10-60 seconds with four parallel processes per host before the botnet moved on to the next target.
The archive also shows these malicious Python scripts relied on private SSH keys belonging to Huge Networks’s CEO, Erick Nascimento. Reached for comment about the files, Mr. Nascimento said he did not write the attack programs and that he didn’t realize the extent of the DDoS campaigns until contacted by KrebsOnSecurity.
“We received and notified many Tier 1 upstreams regarding very very large DDoS attacks against small ISPs,” Nascimento said. “We didn’t dig deep enough at the time, and what you sent makes that clear.”
Nascimento said the unauthorized activity is likely related to a digital intrusion first detected in January 2026 that compromised two of the company’s development servers, as well as his personal SSH keys. But he said there’s no evidence those keys were used after January.
“We notified the team in writing the same day, wiped the boxes, and rotated keys,” Nascimento said, sharing a screenshot of a January 11 notification from Digital Ocean. “All documented internally.”
Mr. Nascimento said Huge Networks has since engaged a third-party network forensics firm to investigate further.
“Our working assessment so far is that this all started with a single internal compromise — one pivot point that gave the attacker downstream access to some resources, including a legacy personal droplet of mine,” he wrote.
“The compromise happened through a bastion/jump server that several people had access to,” Nascimento continued. “Digital Ocean flagged the droplet on January 11 — compromised due to a leaked SSH key, in their wording — I was traveling at the time and addressed it on return. That droplet was deprecated and destroyed, and it was never part of Huge Networks infrastructure.”
The malicious software that powers the botnet of TP-Link devices used in the DDoS attacks on Brazilian ISPs is based on Mirai, a malware strain that made its public debut in September 2016 by launching a then record-smashing DDoS attack that kept this website offline for four days. In January 2017, KrebsOnSecurity identified the Mirai authors as the co-owners of a DDoS mitigation firm that was using the botnet to attack gaming servers and scare up new clients.
In May 2025, KrebsOnSecurity was hit by another Mirai-based DDoS that Google called the largest attack it had ever mitigated. That report implicated a 20-something Brazilian man who was running a DDoS mitigation company as well as several DDoS-for-hire services that have since been seized by the FBI.
Nascimento flatly denied being involved in DDoS attacks against Brazilian operators to generate business for his company’s services.
“We don’t run DDoS attacks against Brazilian operators to sell protection,” Nascimento wrote in response to questions. “Our sales model is mostly inbound and through channel integrator, distributors, partners — not active prospecting based on market incidents. The targets in the scripts you received are small regional providers, the vast majority of which are neither in our customer base nor in our commercial pipeline — a fact verifiable through public sources like QRator.”
Nascimento maintains he has “strong evidence stored on the blockchain” that this was all done by a competitor. As for who that competitor might be, the CEO wouldn’t say.
“I would love to share this with you, but it could not be published as it would lose the surprise factor against my dishonest competitor,” he explained. “Coincidentally or not, your contact happened a week before an important event – one that this competitor has NEVER participated in (and it’s a traditional event in the sector). And this year, they will be participating. Strange, isn’t it?”
Strange indeed.
The Linux Link Tech Show Episode 1135
SN 1076: FAST16.SYS - Unmasking the NSA's Most Diabolical Digital Sabotage
What if your engineering calculations secretly sabotaged your nation's best efforts? This week, we reveal how a newly uncovered 21-year-old NSA rootkit quietly corrupted scientific research in hostile states and why it changes everything you think you know about cyberwarfare.
- Bitwarden's CLI hit with a supply-chain attack.
- Commercial routers in Iran fail shortly before the war.
- Meta logging all employee activity to train replacement AI.
- GRC's DNS Benchmark Release 5.
- Two miscellaneous AI thoughts.
- A bunch of terrific listener feedback.
- Unraveling the diabolical history of "fast16.sys"
Show Notes - https://www.grc.com/sn/SN-1076-Notes.pdf
Hosts: Steve Gibson and Leo Laporte
Download or subscribe to Security Now at https://twit.tv/shows/security-now.
You can submit a question to Security Now at the GRC Feedback Page.
For 16kbps versions, transcripts, and notes (including fixes), visit Steve's site: grc.com, also the home of the best disk maintenance and recovery utility ever written Spinrite 6.
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
TWiT 1081: That's Miasma - John Ternus Replacing Tim Cook as Apple CEO
Tim Cook's surprise departure shakes Apple just as AI and product strategy take center stage, sending big questions through Silicon Valley about what comes next. From Toyota's camera-filled Woven City to questionable US police tracking and a Signal privacy gap, this episode digs into how quietly surveillance tech is encroaching on daily life.
- Toyota Woven City
- Tim Cook to become Apple Executive Chairman; John Ternus to become Apple CEO
- Continuous glucose monitoring made me continuously crazy
- Meta will lay off 10% of its workforce, the company told staff today
- Meta projected $16 billion in scam ad revenue. Now the lawsuits are piling up.
In another wild turn for AI chips, Meta signs deal for millions of Amazon AI CPUs
Google is investing up to $40 billion in a company that is beating Gemini. That is the point. - OpenAI Releases 'Spud' GPT-5.5 Model
- China's DeepSeek previews new AI model a year after jolting US rivals
Now we know who paid $100,000 to unlock a Sam Altman podcast interview - Scoop: NSA using Anthropic's Mythos despite Defense Department blacklist
- Anthropic: No "kill switch" for AI in classified settings
- Mozilla Used Anthropic's Mythos to Find and Fix 271 Bugs in Firefox
- Unauthorized group has gained access to Anthropic's exclusive cyber tool Mythos, report claims
- What smart people are saying about SpaceX's $60 billion deal with Cursor: 'The Hunger Games have just begun'
- Australia's Teen Social Media Ban Isn't Working. Half Their Teens Still Have Access, Survey Finds
- Apple fixes bug that cops used to extract deleted chat messages from iPhones
- Nevada Police Can Now Track Cellphones Without a Warrant
- Brussels launched an age checking app. Hackers took 2 minutes to break it
- 'Scattered Spider' Member 'Tylerb' Pleads Guilty
- Iran claims US used backdoors in networking equipment
- The Onion has agreed to a new deal to take over Infowars
- 'Hairdryer used to trick weather sensor' to win $34,000 bet
- To buy this Bay Area home, you'll need Anthropic equity | TechCrunch
- This Alberta Startup Sells No-Tech Tractors for Half Price
- The Hottest Phone for Kids Right Now Is a $100 Landline
- This pasta sauce wants to record your family
Host: Leo Laporte
Guests: Sam Abuelsamid, Victoria Song, and Stacey Higginbotham
Download or subscribe to This Week in Tech at https://twit.tv/shows/this-week-in-tech
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
SN 1075: Yes. Exactly. - The Zero-Day Ticking Clock
Security leaders warn the era of AI-driven bug hunting has arrived, with Mythos uncovering hundreds of overlooked vulnerabilities in code bases as trusted as Firefox. Are defenders ready for the avalanche of exploits and the frantic race to patch?
- A disgruntled developer discloses multiple Windows 0-days.
- Microsoft purchases its own bugs in massive campaign.
- VeraCrypt & Wireshark suddenly lost their dev accounts.
- A serious problem with re-captured domain names.
- How might AI help to secure open source repositories.
- A listener wonders what we thought of Project Hail Mary.
- Cyber security professionals tell us What Mythos Means
Show Notes - https://www.grc.com/sn/SN-1075-Notes.pdf
Hosts: Steve Gibson and Leo Laporte
Download or subscribe to Security Now at https://twit.tv/shows/security-now.
You can submit a question to Security Now at the GRC Feedback Page.
For 16kbps versions, transcripts, and notes (including fixes), visit Steve's site: grc.com, also the home of the best disk maintenance and recovery utility ever written Spinrite 6.
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
‘Scattered Spider’ Member ‘Tylerb’ Pleads Guilty
A 24-year-old British national and senior member of the cybercrime group “Scattered Spider” has pleaded guilty to wire fraud conspiracy and aggravated identity theft. Tyler Robert Buchanan admitted his role in a series of text-message phishing attacks in the summer of 2022 that allowed the group to hack into at least a dozen major technology companies and steal tens of millions of dollars worth of cryptocurrency from investors.
Buchanan’s hacker handle “Tylerb” once graced a leaderboard in the English-language criminal hacking scene that tracked the most accomplished cyber thieves. Now in U.S. custody and awaiting sentencing, the Dundee, Scotland native is facing the possibility of more than 20 years in prison.

Two photos published in a Daily Mail story dated May 3, 2025 show Buchanan as a child (left) and as an adult being detained by airport authorities in Spain. “M&S” in this screenshot refers to Marks & Spencer, a major U.K. retail chain that suffered a ransomware attack last year at the hands of Scattered Spider.
Scattered Spider is the name given to a prolific English-speaking cybercrime group known for using social engineering tactics to break into companies and steal data for ransom, often impersonating employees or contractors to deceive IT help desks into granting access.
As part of his guilty plea, Buchanan admitted conspiring with other Scattered Spider members to launch tens of thousands of SMS-based phishing attacks in 2022 that led to intrusions at a number of technology companies, including Twilio, LastPass, DoorDash, and Mailchimp.
The group then used data stolen in those breaches to carry out SIM-swapping attacks that siphoned funds from individual cryptocurrency investors. In an unauthorized SIM-swap, crooks transfer the target’s phone number to a device they control and intercept any text messages or phone calls to the victim’s device — such as one-time passcodes for authentication and password reset links sent via SMS. The U.S. Justice Department said Buchanan admitted to stealing at least $8 million in virtual currency from individual victims throughout the United States.
FBI investigators tied Buchanan to the 2022 SMS phishing attacks after discovering the same username and email address was used to register numerous phishing domains seen in the campaign. The domain registrar NameCheap found that less than a month before the phishing spree, the account that registered those domains logged in from an Internet address in the U.K. FBI investigators said the Scottish police told them the address was leased to Buchanan throughout 2022.
As first reported by KrebsOnSecurity, Buchanan fled the United Kingdom in February 2023, after a rival cybercrime gang hired thugs to invade his home, assault his mother, and threaten to burn him with a blowtorch unless he gave up the keys to his cryptocurrency wallet. That same year, U.K. investigators found a device at Buchanan’s Scotland residence that included data stolen from SMS phishing victims and seed phrases from cryptocurrency theft victims.
Buchanan was arrested by Spanish authorities in June 2024 while trying to board a flight to Italy. He was extradited to the United States and has remained in U.S. federal custody since April 2025.
Buchanan is the second known Scattered Spider member to plead guilty. Noah Michael Urban, 21, of Palm Coast, Fla., was sentenced to 10 years in federal prison last year and ordered to pay $13 million in restitution. Three other alleged co-conspirators — Ahmed Hossam Eldin Elbadawy, 24, a.k.a. “AD,” of College Station, Texas; Evans Onyeaka Osiebo, 21, of Dallas, Texas; and Joel Martin Evans, 26, a.k.a. “joeleoli,” of Jacksonville, North Carolina – still face criminal charges.
Two other alleged Scattered Spider members will soon be tried in the United Kingdom. Owen Flowers, 18, and Thalha Jubair, 20, are facing charges related to the hacking and extortion of several large U.K. retailers, the London transit system, and healthcare providers in the United States. Both have pleaded not guilty, and their trial is slated to begin in June.
Investigators say the Scattered Spider suspects are part of a sprawling cybercriminal community online known as “The Com,” wherein hackers from different cliques boast publicly on Telegram and Discord about high-profile cyber thefts that almost invariably begin with social engineering — tricking people over the phone, email or SMS into giving away credentials that allow remote access to corporate internal networks.
One of the more popular SIM-swapping channels on Telegram has long maintained a leaderboard of the most rapacious SIM-swappers, indexed by their supposed conquests in stealing cryptocurrency. That leaderboard previously listed Buchanan’s hacker alias Tylerb at #65 (out of 100 hackers), with Urban’s moniker “Sosa” coming in at #24.
Buchanan’s sentencing hearing is scheduled for August 21, 2026. According to the Justice Department, he faces a statutory maximum sentence of 22 years in federal prison. However, any sentence the judge hands down in this case may be significantly tempered by a number of mitigating factors in the U.S. Sentencing Guidelines, including the defendant’s age, criminal history, time already served in U.S. custody, and the degree to which they cooperated with federal authorities.
TWiT 1080: Destroy All Phonorecords - Musk v. Altman, Claude Opus 4.7, & Voyager 1
As Anthropic, OpenAI, and industry giants race to outpace each other, data centers and supply chains are straining, while job markets and open-source communities feel the heat. Listen in for a roundtable on whether AI is fueling innovation, burnout, or just the next tech bubble.
- Anthropic releases Claude Opus 4.7, concedes it trails unreleased Mythos
- Nobody knows how many CVEs Anthropic's Project Glasswing has actually found
- You're About to See a Lot of Critical Software Updates. Don't Ignore Them.
- Cal.com Is Going Closed Source Because of AI
- AI anxiety is turning volatile
- Humanoid robots race past humans in Beijing half-marathon, showing rapid advances
- Snap Is Laying Off 16% of Full-Time Staff as It Embraces A.I.
- Musk v. Altman Is a Battle for OpenAI's Soul
- The Little Probe That Could: Why Voyager 1 Matters, and Why NASA Just Switched Part of It Off
- Sam Altman's project World looks to scale its human verification empire. First stop: Tinder.
- Meta Must Face Youth Addiction Lawsuit by Massachusetts, Court Rules
- Section 230 Is Dying By A Thousand Workarounds, And Massachusetts Just Added Another One
- Live Nation and Ticketmaster lose monopoly case
- Anna's Archive told to pay Spotify and record labels $322 million over unprecedented music scraping
- Roblox agrees to a $12 million settlement with Nevada
- Judge sides with creators of banned ICE trackers who allege DHS and DOJ violated their First Amendment rights
- What's the point of the App Store, if it can't protect users?
- TotalRecall Reloaded tool finds a side entrance to Windows 11's Recall database
- Google, Microsoft, Meta All Tracking You Even When You Opt Out, According to an Independent Audit
- It Is Time to Ban the Sale of Precise Geolocation
- Google Broke Its Promise to Me. Now ICE Has My Data. | Electronic Frontier Foundation
- Billionaire Netflix cofounder Reed Hastings is leaving the company
- Venture capitalist Ron Conway says he is starting treatment for a 'rare' cancer
Host: Leo Laporte
Guests: Louis Maresca, Wesley Faulkner, and Glenn Fleishman
Download or subscribe to This Week in Tech at https://twit.tv/shows/this-week-in-tech
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
SN 1074: What Mythos Means - Marketing or Mayhem
We may already be living through the most consequential hundred days in cyber history, and the arrival of AI that can autonomously chain zero-day vulnerabilities into working exploits means the software industry's long-standing "ship it and patch it later" era is officially over.
Show Notes - https://www.grc.com/sn/SN-1074-Notes.pdf
Hosts: Steve Gibson and Leo Laporte
Download or subscribe to Security Now at https://twit.tv/shows/security-now.
You can submit a question to Security Now at the GRC Feedback Page.
For 16kbps versions, transcripts, and notes (including fixes), visit Steve's site: grc.com, also the home of the best disk maintenance and recovery utility ever written Spinrite 6.
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
Patch Tuesday, April 2026 Edition
Microsoft today pushed software updates to fix a staggering 167 security vulnerabilities in its Windows operating systems and related software, including a SharePoint Server zero-day and a publicly disclosed weakness in Windows Defender dubbed “BlueHammer.” Separately, Google Chrome fixed its fourth zero-day of 2026, and an emergency update for Adobe Reader nixes an actively exploited flaw that can lead to remote code execution.

Redmond warns that attackers are already targeting CVE-2026-32201, a vulnerability in Microsoft SharePoint Server that allows attackers to spoof trusted content or interfaces over a network.
Mike Walters, president and co-founder of Action1, said CVE-2026-32201 can be used to deceive employees, partners, or customers by presenting falsified information within trusted SharePoint environments.
“This CVE can enable phishing attacks, unauthorized data manipulation, or social engineering campaigns that lead to further compromise,” Walters said. “The presence of active exploitation significantly increases organizational risk.”
This flaw drops alongside a separate SQL Server remote code execution vulnerability (CVE-2026-33120), notes Ryan Braunstein, manager of Security and IT at Automox.
“One bug allows an attacker to get into your SQL instance from the network,” Braundstein said. “The other lets someone already inside promote themselves to full control.”
Microsoft also addressed BlueHammer (CVE-2026-33825), a privilege escalation bug in Windows Defender. According to BleepingComputer, the researcher who discovered the flaw published exploit code for it after notifying Microsoft and growing exasperated with their response. Will Dormann, senior principal vulnerability analyst at Tharros, says he confirmed that the public BlueHammer exploit code no longer works after installing today’s patches.
Satnam Narang, senior staff research engineer at Tenable, said April marks the second-biggest Patch Tuesday ever for Microsoft. Narang also said there are indications that a zero-day flaw Adobe patched in an emergency update on April 11 — CVE-2026-34621 — has seen active exploitation since at least November 2025.
Adam Barnett, lead software engineer at Rapid7, called the patch total from Microsoft today “a new record in that category” because it includes nearly 60 browser vulnerabilities. Barnett said it might be tempting to imagine that this sudden spike was tied to the buzz around the announcement a week ago today of Project Glasswing — a much-hyped but still unreleased new AI capability from Anthropic that is reportedly quite good at finding bugs in a vast array of software.
But he notes that Microsoft Edge is based on the Chromium engine, and the Chromium maintainers acknowledge a wide range of researchers for the vulnerabilities which Microsoft republished last Friday.
“A safe conclusion is that this increase in volume is driven by ever-expanding AI capabilities,” Barnett said. “We should expect to see further increases in vulnerability reporting volume as the impact of AI models extend further, both in terms of capability and availability.”
Finally, no matter what browser you use to surf the web, it’s important to completely close out and restart the browser periodically. This is really easy to put off (especially if you have a bajillion tabs open at any time) but it’s the only way to ensure that any available updates get installed. For example, a Google Chrome update released earlier this month fixed 21 security holes, including the high-severity zero-day flaw CVE-2026-5281.
For a clickable, per-patch breakdown, check out the SANS Internet Storm Center Patch Tuesday roundup. Running into problems applying any of these updates? Leave a note about it in the comments below and there’s a decent chance someone here will pipe in with a solution.
TWiT 1079: Fans. Only Fans. - Is Mythos Preview Too Powerful for Public Release?
Anthropic has built an AI model so sharp it's being withheld from the public, sparking debate over who gets access to world-changing tech and who's left behind. Hear how this "too dangerous" AI could tip the balance for the world's most powerful players. This episode unpacks the fresh moral minefields created when cutting-edge tech collides with politics, security, and human lives.
- Anthropic says its most powerful AI cyber model is too dangerous to release publicly — so it built Project Glasswing
- Sam Altman Fire Bombing Response
- OpenAI Backs Bill That Would Limit Liability for AI-Enabled Mass Deaths or Financial Disasters
- Samsung flags eightfold jump in quarterly profit as AI chip demand pumps prices
- SpaceX Posted Nearly $5 Billion Loss Last Year from AI Spending
- Trump administration plans to cut cybersecurity agency's budget by $700 million
- CPUID hijacked to serve malware as HWMonitor downloads
- GTA 6 Developer Rockstar Reportedly Hacked, Data Being Ransomed
- FBI used iPhone notification data to retrieve deleted Signal messages - 9to5Mac
- ICE acknowledges it is using powerful spyware
- Helium Is Hard to Replace
- John Deere to Pay $99 Million in Monumental Right-to-Repair Settlement
- France's government is ditching Windows for Linux, calling US tech dependence a strategic risk
- The disturbing white paper Red Hat is trying to erase from the internet
- DOJ Top Antitrust Litigators Exit After Ticketmaster Settlement
- My Quest to Solve Bitcoin's Great Mystery
- Bitcoin miners are losing $19,000 on every BTC produced as difficulty drops 7.8%
- 'Abhorrent': the inside story of the Polymarket gamblers betting millions on war
Host: Leo Laporte
Guests: Doc Rock, Jason Hiner, and Mike Elgan
Download or subscribe to This Week in Tech at https://twit.tv/shows/this-week-in-tech
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
SN 1073: The FCC Bans New Consumer Routers - LinkedIn's JavaScript Bombshell
The FCC has banned all new consumer routers made outside the US, leaving networks stuck with aging, insecure hardware while blocking innovation. Find out why this sweeping move is raising eyebrows and lawsuits—and why it makes zero sense for cybersecurity.
- Will California require Linux to verify its user's age.
- Apple's iOS 26.4 requires UK users to prove their age.
- Russia chooses to use home grown 5G mobile encryption.
- Ukraine knew the webcam was installed by Russian spies.
- Google moves quantum computing "Q Day" to 2029.
- At RSA, UK's NCSC CEO warns of vibe-coded SaaS replacements.
- More information about nasty ClickFix campaigns.
- More than one in seven Reddit postings are an AI-bot.
- The story behind the LiteLLM disaster that was averted
Show Notes - https://www.grc.com/sn/SN-1073-Notes.pdf
Hosts: Steve Gibson and Leo Laporte
Download or subscribe to Security Now at https://twit.tv/shows/security-now.
You can submit a question to Security Now at the GRC Feedback Page.
For 16kbps versions, transcripts, and notes (including fixes), visit Steve's site: grc.com, also the home of the best disk maintenance and recovery utility ever written Spinrite 6.
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
Russia Hacked Routers to Steal Microsoft Office Tokens
Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code.
Microsoft said in a blog post today it identified more than 200 organizations and 5,000 consumer devices that were caught up in a stealthy but remarkably simple spying network built by a Russia-backed threat actor known as “Forest Blizzard.”

How targeted DNS requests were redirected at the router. Image: Black Lotus Labs.
Also known as APT28 and Fancy Bear, Forest Blizzard is attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU). APT 28 famously compromised the Hillary Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee in 2016 in an attempt to interfere with the U.S. presidential election.
Researchers at Black Lotus Labs, a security division of the Internet backbone provider Lumen, found that at the peak of its activity in December 2025, Forest Blizzard’s surveillance dragnet ensnared more than 18,000 Internet routers that were mostly unsupported, end-of-life routers, or else far behind on security updates. A new report from Lumen says the hackers primarily targeted government agencies—including ministries of foreign affairs, law enforcement, and third-party email providers.
Black Lotus Security Engineer Ryan English said the GRU hackers did not need to install malware on the targeted routers, which were mainly older Mikrotik and TP-Link devices marketed to the Small Office/Home Office (SOHO) market. Instead, they used known vulnerabilities to modify the Domain Name System (DNS) settings of the routers to include DNS servers controlled by the hackers.
As the U.K.’s National Cyber Security Centre (NCSC) notes in a new advisory detailing how Russian cyber actors have been compromising routers, DNS is what allows individuals to reach websites by typing familiar addresses, instead of associated IP addresses. In a DNS hijacking attack, bad actors interfere with this process to covertly send users to malicious websites designed to steal login details or other sensitive information.
English said the routers attacked by Forest Blizzard were reconfigured to use DNS servers that pointed to a handful of virtual private servers controlled by the attackers. Importantly, the attackers could then propagate their malicious DNS settings to all users on the local network, and from that point forward intercept any OAuth authentication tokens transmitted by those users.
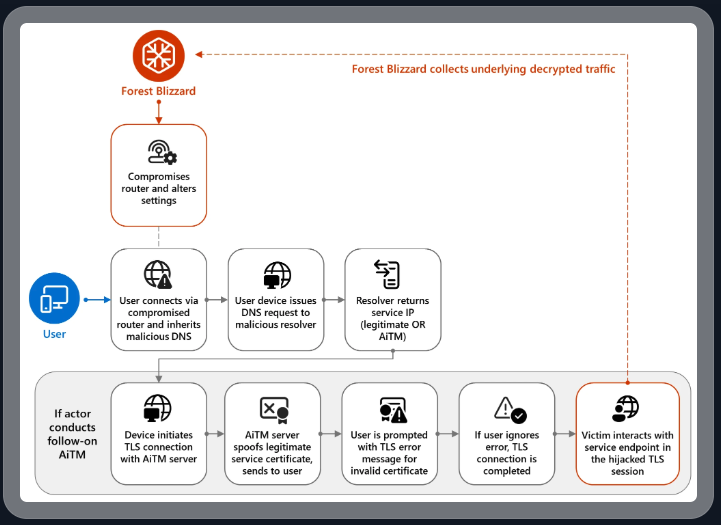
DNS hijacking through router compromise. Image: Microsoft.
Because those tokens are typically transmitted only after the user has successfully logged in and gone through multi-factor authentication, the attackers could gain direct access to victim accounts without ever having to phish each user’s credentials and/or one-time codes.
“Everyone is looking for some sophisticated malware to drop something on your mobile devices or something,” English said. “These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done.”
Microsoft refers to the Forest Blizzard activity as using DNS hijacking “to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains.” The software giant said while targeting SOHO devices isn’t a new tactic, this is the first time Microsoft has seen Forest Blizzard using “DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices.”
Black Lotus Labs engineer Danny Adamitis said it will be interesting to see how Forest Blizzard reacts to today’s flurry of attention to their espionage operation, noting that the group immediately switched up its tactics in response to a similar NCSC report (PDF) in August 2025. At the time, Forest Blizzard was using malware to control a far more targeted and smaller group of compromised routers. But Adamitis said the day after the NCSC report, the group quickly ditched the malware approach in favor of mass-altering the DNS settings on thousands of vulnerable routers.
“Before the last NCSC report came out they used this capability in very limited instances,” Adamitis told KrebsOnSecurity. “After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable.”